According to an IBM study, the average cost of a ransomware attack (all ransomware is malware) is $4.54 million. Here, we will discuss what Malware is, its types, and security tips to protect yourself from Malware attacks.
The term Malware was first used in 1990 by computer scientist Yisrael Radai. Malware is a common term that’s used for any malicious program or code that affects systems. Malware is termed as malicious software too. To be specific, types of malware include ransomware, trojans, spyware, adware, and worms. Each has its own form and act differently, but the common thing between them is that they all can put your business at risk.
In this article, we are going to inform you about the actions you can take to secure your business from malware. Also, we will let you know who’s at the risk of malware, types of malware and provide unbiased information on top tips to prevent business against malware
What is Malware?
Malware refers to malicious files and programs designed to cause extensive damage to a website or application. Any business, no matter how small, medium, or large, can be affected by it.
We are all aware of cybercriminals’ activities, and cyberattacks are becoming a universal concern. Also, cyber actors are very creative in developing more and more devious ways to deposit malware into their targeted spaces.
Due to the data loss, operational downtime, and reputational damage caused by cyberattacks, it is crucial to take safety measures to ensure that everything is protected from malware attacks.
Let’s learn the most common types of malware attacks.
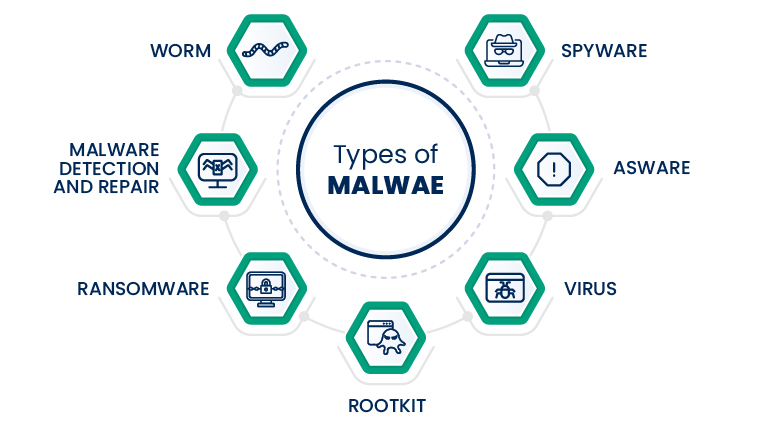
Virus: A virus can replicate itself and spread into a computer system. When a site runs, the virus comes into action. Once the virus is activated, it starts to multiply and propagate the infection in the system. A virus can send off itself to additional computer systems in the same network.
Trojan: Trojan comes in the form of software updates or app updates. Once software that includes trojan inside gets updated, the trojan is also installed along with it. It can lead to other types of attacks including ransomware, spyware, Cryptojacking malware, etc.
Worm: A worm does not require any host program and human interaction or any instruction from a malware author. A worm is perilous as it can replicate, spread and multiply without any help. Once it is propagated, it is hard to stop it.
Spyware: Spyware silently works on a computer system and gathers users’ details without their understanding. The details could be passwords, PINs, payment information, or any messages. By collecting the information, cyber thieves monitor users’ behavior and different activities.
Adware: Adware monitors users’ surfing activity and presents specific ads to the user. The details collected by adware include the user’s browsing history, search history, social interactions on different sites, shopping fondness, cart information. The information then sells to advertisers or shows targeted ads.
Ransomware: Ransomware is the most profitable technique of malware. Cybercriminals install ransomware on a user’s computer system and encode files and other data then ask for a ransom amount to unlock a user’s data and files. Cybercriminals in a few cases, transfer the data to a server that they can control and use it.
Cryptojacking Malware: Cybercriminal hacks into the computer system and installs the software. Software consumes the power and resources of the system to mine cryptocurrencies. It can steal cryptocurrency wallets. Cryptojacking uses a code that is hard to detect and runs in the background.
Botnet Malware: Cybercriminals use a bot to infect a group of computers and use them for a malicious flood attack. A botnet is a self-disseminated malware that connects back to the main server. Bots formed in huge numbers called a botnet. A botnet exploits the vulnerability and can spread to millions of computers. It can interrupt the supply chain, steal sensitive information, and create disruption.
How Does Malware Spread?
There are many ways that malware can infect your system. The following are a few examples:
- Downloading software or an app that’s malicious
- Downloading legit software that’s bundled with malware
- Visiting a malicious website
- Clicking on a fake pop-up window that leads to a malware download
- Unboxing a malicious email that contains malware
Ultimately, there are many ways malware can be spread, but that doesn’t mean you can’t stop it. Here, we will discuss some security tips to help you prevent malware attacks.
How to Prevent Malware Attacks – Top 10 Security Tips
-
Use Antivirus Software
Antivirus software scans detect and fix viruses, worms, and other types of malware that could infect the computer system. Antivirus scans each file for malware or viruses that relates to the web world.
It is wise to update the signature of the antivirus regularly as antivirus authors release frequent updates and fix patches against the latest malware and bugs in a program. The latest update ensures that a user will not distribute the malware accidentally to the website. So, thinking of how to prevent malware attacks, these are the first tips to follow.
-
Use Encryption to Secure Data in Transit
To enable encryption on the website, it is necessary to go with an SSL certificate. SSL means Secure Socket Layer. SSL certificate encrypts ongoing information between the server and the browser hence, a third party can not intercept the communication occurring between two ends.
-
Use Secure Authentication Methods
To secure a network, a few authentication methods are necessary. Multi-factor authentication (MFA), a strong password can be considered a secure authentication method.
MFA involves two verification steps to access any application, VPN, or online account. It is a part of a strong identity and access management policy. This authentication method reduces the chance of malware attacks.
-
Do not allow file upload on the website
A malicious actor can misuse your server and upload a malicious script on the server. It is wise to avoid executable permissions for files, images, or any type of documents. There are huge chances of infecting the website with nasty malware. There should be another way for users on the website to share the files.
-
Use Form Validation
Form validation is quite necessary as it can block malicious scripts from running via form fields. Improper form validation can cause malware attacks including header injection, XSS-site scripting, SQL injection.
-
Protect Against SQL Injection Attack
Developers or system admin can keep plugins, frameworks, and libraries up to date with the latest patches. The system admin should not connect web applications to the database with admin rights. It is also sensible not to share shared database accounts among websites or apps.
-
Protect Against XSS Attacks
XSS attack or Cross-Site Scripting attack is a client-side code injection. An attacker carries out a malicious script in a browser with malicious code residing in a valid site or application.
The attack begins when a user visits an untrusted web page or app. To overcome this situation, you should install a firewall, sanitize input data, and validate input user data.
-
Install Firewall
For Malware Prevention, a Web Application Firewall (WAF) is necessary to install on the system. It is designed to safeguard web applications, mobile apps, and APIs by removing HTTP traffic coming between a web application and the web.
The WAF follows the OSI model to prevent malicious traffic and thereby avert web application attacks. A firewall filters traffic related to IP and ports. A firewall enables a higher level of security to prevent malware attacks.
-
Take Backups
Admin should update WordPress plugins, theme, CMS, and framework frequently. Attackers always try to find an unpatched system as it seems a soft target to enter the system.
-
Logout From Website
It is sensible to log out of a site when you complete the work to avert a third party to access the system without validating credentials. You can add a session management script that will automatically log out at a certain time.
Conclusion
The best practice to get rid of malware is to stop what you are doing when your system is suspected of having malware. Yes, working on or continuing to use an infected system may spread the malware further, and that can be dangerous.
It is necessary to know how to prevent malware attacks and stay safe. There is proper training required to detect and avoid malware attacks. A strong security defense and cyber awareness is a critical part of training. Few preventive measures as discussed above can stop potential malware attacks.


