When the CA/Browser Forum passed Ballot SC-081v3 in April 2025, it set one universal deadline March 15, 2026, for all publicly trusted TLS certificates to comply with the new 200-day maximum validity period. What it didn’t dictate was how each Certificate Authority would get there.
The result is that the same rule looks noticeably different depending on which CA issued your certificate.
This post focuses specifically on those CA-level differences, what each CA actually did, when, and what that means for your certificates specifically.
Why the Same Mandate Plays Out Differently Across CAs
The CA/B Forum sets the rules, but CAs have discretion in how and when they enforce them; as long as they comply by the mandatory date. That discretion, combined with differences in customer base, billing infrastructure, and technical architecture, is why enforcement looks different across providers.
Some CAs moved early to eliminate edge-case risk around time zones and issuance windows. Others waited until closer to the deadline. Some issued at exactly 199 days rather than 200 to build in a one-day buffer. It’s also worth noting that the 200-day rule only applies to publicly trusted TLS certificates, internal PKI and privately issued certificates are not affected by this mandate.
How Each CA Is Handling the 200-Day Limit
| CA / Brand | Enforcement Date | Key Differentiator |
|---|---|---|
| DigiCert | Feb 24, 2026 | Earliest enforcer; CertCentral API auto-adjusted; MyP preserved |
| Sectigo / Comodo | Mar 12, 2026 | “6-month cert” framing; proactive 2027 guidance |
| GlobalSign | Mar 14, 2026 | Simultaneous root migration to TLS-dedicated roots |
| GeoTrust / Thawte / RapidSSL | Feb 24, 2026 | DigiCert infrastructure; follow DigiCert’s enforcement date |
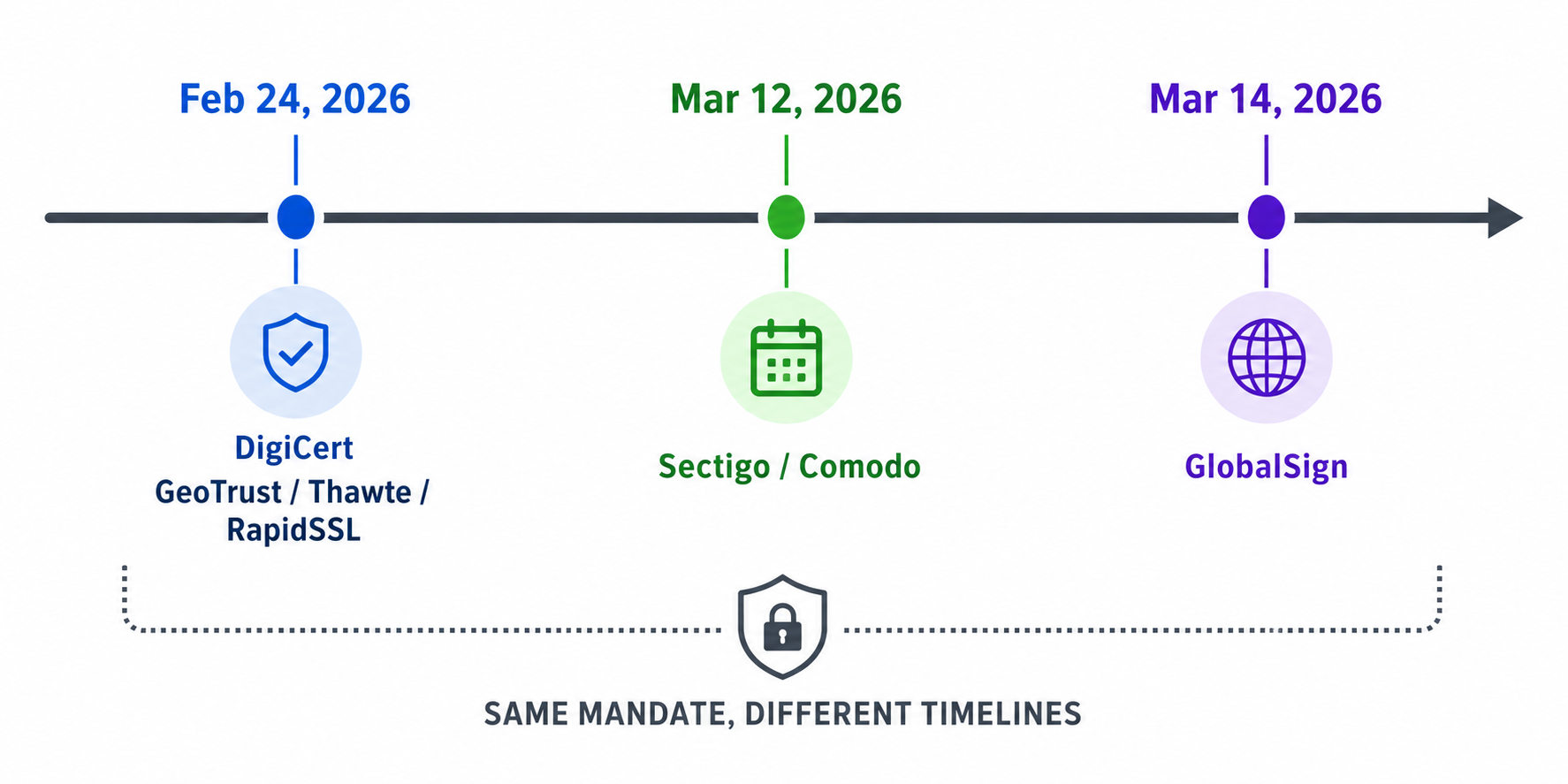
DigiCert — The Earliest Enforcer
DigiCert enforced the 199-day cap on February 24, 2026, nearly three weeks before the mandatory deadline. The one-day gap from 200 to 199 was intentional; it eliminates any risk of a certificate technically exceeding the CA/B Forum’s hard limit due to time-zone differences at the moment of issuance.
All public TLS certificates from DigiCert including DV, OV, and EV, fall under the cap, determined by issuance date, not purchase date. So, if an order was placed before February 24 but the certificate wasn’t issued until after, the 199-day limit applies.
OV customers got an additional change on the same date. The organization validation reuse period was shortened from 825 days to 397 days. If your OV certificate was relying on organization data validated more than a year ago, revalidation was required before your next issuance, on a separate schedule from domain validation.
Multi-Year Plan holders keep their coverage intact, with certificates continuing to reissue at no extra cost until the plan expires. DigiCert also adjusted CertCentral’s API so requests submitted with validity over 199 days are automatically corrected rather than rejected, preventing broken integrations for API users without requiring any changes on their end.
Sectigo — Practical Framing, Early Compliance
Sectigo enforced the cap on March 12, 2026, three days before the deadline. Rather than leading with compliance language, they told customers to reframe these as six-month certificates and recommended renewing at day 180. It leaves a buffer for domain validation, CSR generation, and deployment without cutting it to the wire.
For wildcard and multi-domain certificates, the shorter validity period has an amplified effect. A single wildcard covers every subdomain under a domain, so a missed renewal takes all of them down simultaneously. That risk isn’t new, but with renewals happening twice as often, the margin for error shrinks accordingly.
GlobalSign — Two Overlapping Changes in 2026
GlobalSign enforced the cap on March 14, 2026. Domain and IP validation reuse is now limited to 200 days; OV and EV organization data reuse is capped at 398 days.
What separates GlobalSign from other CAs this year is a simultaneous root migration. Their existing roots, R3, R5, and R6 are multi-purpose roots shared across TLS, code signing, and email certificates. Browser policies are moving toward purpose-specific roots, requiring GlobalSign to migrate to dedicated TLS roots: R46 and E46.
There’s a hard deadline embedded in this that intersects directly with the validity change: certificates issued under Root R3 must be issued before August 27, 2026 to remain fully trusted for their entire 200-day lifetime. From July 27, 2026, all products move to the new TLS-dedicated roots, with cross-certificates provided to maintain browser compatibility during transition.
GeoTrust, Thawte, and RapidSSL — Following DigiCert’s Timeline
GeoTrust, Thawte, and RapidSSL are all issued through DigiCert’s infrastructure, which means they followed DigiCert’s February 24 enforcement date. The brands are different, but the underlying CA system is same.
If your certificate from any of these three was issued before February 24, you received up to 397 days of validity. Anything issued from that date onward is capped at 199 days regardless of which brand you selected.
RapidSSL is worth a specific mention. Its customer base skews toward manual certificate management; it’s a popular low-cost DV option precisely because setup is simple. Doubling the renewal frequency hits that segment harder than enterprise buyers already running structured workflows. Multi-year plan holders across all three brands continue reissuing at no extra cost, with each certificate now capped at 199 days.
Choosing the Right CA on CheapSSLShop for the 200-Day Era
The 199-day cap applies to every CA equally, but the right choice still depends on what you’re protecting and how you’re managing it.
If you’re running a single domain or a small number of sites, RapidSSL or PositiveSSL remain the most straightforward entry points with low cost and fast DV issuance. Just account for two manual renewals per year in your calendar now rather than one.
For wildcard coverage, Sectigo and Comodo wildcard certificates are solid options, but given that a missed renewal on a wildcard takes down every subdomain at once, following Sectigo’s own advice of renewing at day 180 rather than waiting until expiry is worth taking seriously.
If your site requires OV or EV trust signals, DigiCert EV, Sectigo EV, GeoTrust True BusinessID, and Thawte SSL Web Server OV are all available. With these, track your domain validation and organization validation schedules separately, they expire on different timelines under the new rules.
For multi-domain coverage, Sectigo Multi-Domain and GeoTrust TBID Multi Domain SSL Certificate cover multiple domains under a single certificate; all SANs renew together, which simplifies management even with the shorter validity window.
Across all of these, a multi-year plan is still the most cost-effective structure. You lock in your price upfront and reissue every 199 days within the plan at no extra cost.
Frequently Asked Questions
Does the 200-day rule affect certificates I’ve already purchased?
No. Certificates issued before each CA’s enforcement date retain their original validity and remain trusted until they expire. The new 199-day cap applies to new issuances and reissuances only.
If I buy a multi-year plan on CheapSSLShop, do I still get a full year on my certificate?
From the enforcement dates mentioned above, individual certificates are capped at 199 days regardless of plan length. Multi-year plans still make sense because they lock in pricing and allow free reissuances throughout the plan period. You’ll reissue every 199 days at no extra cost.
Why did DigiCert enforce earlier than the CA/B Forum deadline?
CAs have discretion on timing as long as they meet the mandatory date. DigiCert moved on February 24 to eliminate any risk of a certificate exceeding the 200-day cap due to time-zone edge cases on the enforcement date itself. It’s a risk management call rather than anything competitive.
Does the 200-day rule apply to wildcard SSL certificates?
Yes. Wildcard certificates are subject to the same 199-day cap. Because a single wildcard covers all subdomains under a domain; a missed renewal affects everything under that domain simultaneously — making the shorter validity period particularly high-stakes for wildcard holders.
What to Keep in Mind as a CheapSSLShop Customer
For most buyers, the day-to-day change is more straightforward. Your certificate now lasts approximately six months. Multi-year plans remain the practical choice; the pricing structure works in your favor even with more frequent reissuances, and the reissuance itself doesn’t cost extra. The 100-day phase arrives in March 2027. The time to build a reliable renewal process is now.
Shorter certificate lifecycles are changing how CAs handle issuance, validation, and renewals. Choose an SSL certificate that fits your setup, reduces renewal risk, and keeps deployments consistent as validity windows shrink.
Related Posts: